 Written by: Jen Carlevatti // Feb 2, 2021
Written by: Jen Carlevatti // Feb 2, 2021
Last updated: Jan 17, 2023
In the digital age, no organization is immune to cybersecurity threats, but K-12 schools can be especially vulnerable. Incidents were already on the rise prior to the start of the pandemic, and the rapid transition to online learning last spring markedly increased opportunities for mischief. The good news? There are plenty of ways to protect students, staff and systems. We’ll explore the top 5 K-12 cybersecurity threats schools are facing, why they’re occurring, and what can be done to stop attacks in their tracks.
Why Are School Cyberattacks So Prevalent?
According to the 2019 State of Malware report, education is consistently in the top 10 industries targeted by cybercriminals. Why is this so?
U.S. schools are data-rich targets for cybercriminals. Stolen data includes the names, Social Security numbers, and email addresses of students, their academic and health records, financial information, and more. They are a veritable gold mine for hackers.
Also contributing to the problem is a chronic lack of funding in IT infrastructure and few (if any) professional development opportunities surrounding cybersecurity. Many school staff with access to data inadvertently allow bad actors in due to a lack of training.
Lastly, today’s students are incredible tech savvy, but many are not aware of good cyber hygiene practices. Systems are often compromised through carelessness or by students actively seeking ways around security restrictions.

The Dirty Five
While there are myriad ways cyber criminals can worm their way into school systems and create havoc, the five most common include:
5. Phishing Scams
Ever receive an email that looks like it’s from your favorite online retailer asking for your password? You’ve been phished!
According the Malwarebytes LABS, phishing attacks aim to collect personal data — including login credentials, credit card numbers, Social Security numbers, and bank account numbers — for fraudulent purposes.
The attack is most commonly delivered as an email or text that looks like it’s from a legitimate source, such as a bank or online shopping site, but it can also appear to come from an individual of authority (such as a superintendent) or a personal acquaintance. Legitimate organizations will NEVER ask for sensitive personal information via email or text.
What You Can Do
Learn how to spot these phony phishing communications. Some of the most common red flags include:
- The URL shown on the email and the URL that displays when you hover over a link are different from one another.
- The “From” address is an imitation of a legitimate address, especially from a business.
- The formatting and design are different from what you usually receive from an organization.
- The content is badly written or contains spelling and grammatical mistakes.
- The email threatens to close your account or requests an urgent response.
- The email contains attachments from unknown sources that you were not expecting.
Once you’ve identified a phishing communication, delete it immediately. Do not respond with personal information. Do not click on any of the links included. Do not download any attachments.
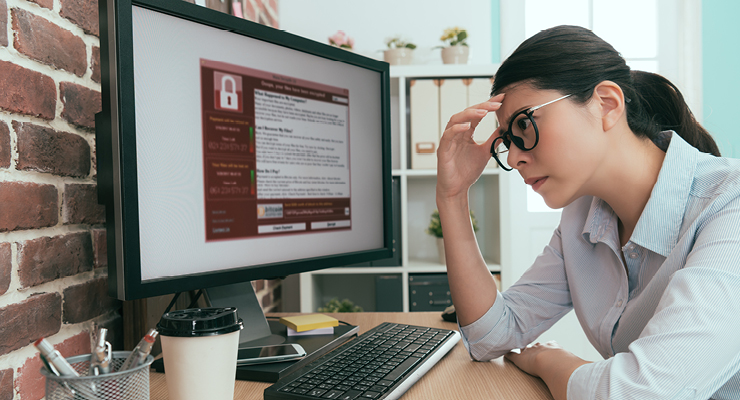
4. Ransomware Attacks
Ransomware is a type of malicious software that encrypts data and requires a ransom to be paid in order to regain access to the data. Cybercriminals also may threaten to release the data unless a ransom is paid. Sometimes e-mails are sent to parents and students with ransom being demanded from the schools.
Unfortunately, these attacks were particularly aggressive in 2020. In August and September, 57 percent of ransomware attacks reported to the U.S. Cybersecurity Infrastructure and Security Agency involved K-12 schools. In one memorable ransomware attack right before Thanksgiving, classes in Baltimore County schools were canceled for more than 115,000 students.
What You Can Do
The advice for preventing ransomware attacks is the same as for phishing scams. In addition:
- Keep your software (particularly anti-virus software) and operating systems up to date.
- Back up data on a regular basis to the cloud or an external drive that you disconnect when not in use.
- Only download from sites you trust.
- Never use unfamiliar USB drives.
- Avoid using public WiFi for confidential transactions (or use a secure VPN).
3. Data Breaches
Between 2016 and 2020, thousands of K-12 students had their personal information compromised as a result of 99 data breaches. Compromised data included grades, bullying reports, and Social Security numbers — leaving students vulnerable to emotional, physical, and financial harm. These breaches occur when a cybercriminal successfully infiltrates a data source and extracts sensitive information.
What You Can Do
There are a number of things your IT department can do to prevent data breaches. On an individual level, be sure to:
- Create strong passwords and protect them religiously.
- Exercise extreme caution with emails (see phishing scams above).
- Treat all devices as capable of accessing school data.
2. Distributed Denial of Service Attacks
This type of school cyberattack occurs when a hacker floods the bandwidth or resources of the school’s servers, thus preventing teachers and students from accessing digital education resources. In some cases, these attacks are an inside job by students looking to avoid attending class or taking a test, as was the case with the 16-year-old Miami student who orchestrated a series of cyberattacks on his school in Sept. 2020.
What You Can Do
Unfortunately, these attacks can’t be prevented. There are steps your IT department can take to anticipate an attack and mitigate its effects, but there isn’t much you can do on an individual level.
1. Zoom Bombing
Zoom bombing is a recent addition to the cyber threat list, and although it’s a funny sounding term, there’s nothing amusing about uninvited guests joining your distance learning session. The actions of these bad actors run the gamut from assaulting students verbally to sharing students’ personal information to displaying violent and/or pornographic images.
What You Can Do
- Don't use your Personal Meeting ID for the meeting. Instead, use a per-meeting ID, exclusive to a single meeting.
- Enable the "Waiting Room" feature so that you can see who is attempting to join the meeting before allowing them access.
- Disable other options, including the ability for others to Join Before Host.
- Once the meeting begins and everyone is in, lock the meeting to outsiders.
Educate Yourself and Fight Back
Want more information on how to reduce cybersecurity threats in your school? USF offers a low-cost cybersecurity course that prepares educators to protect sensitive data and implement cyber hygiene in their teaching. Register today to learn more about safeguarding your school’s information from cyber criminals.


